by
CYBER THREAT INTELLIGENCE
“Martin takes a thorough and focused approach to the processes that rule threat intelligence, but he doesn’t just cover gathering, processing and distributing intelligence. He explains why you should care who is trying to hack you, and what you can do about it when you know.”
―Simon Edwards, Security Testing Expert, CEO SE Labs Ltd., Chair AMTSO
Effective introduction to cyber threat intelligence, supplemented with detailed case studies and after action reports of intelligence on real attacks
Cyber Threat Intelligence introduces the history, terminology, and techniques to be applied within cyber security, offering an overview of the current state of cyberattacks and stimulating readers to consider their own issues from a threat intelligence point of view. The author takes a systematic, system-agnostic, and holistic view to generating, collecting, and applying threat intelligence.
The text covers the threat environment, malicious attacks, collecting, generating, and applying intelligence and attribution, as well as legal and ethical considerations. It ensures readers know what to look out for when considering a potential cyber attack and imparts how to prevent attacks early on, explaining how threat actors can exploit a system’s vulnerabilities. It also includes analysis of large scale attacks such as WannaCry, NotPetya, Solar Winds, VPNFilter, and the Target breach, looking at the real intelligence that was available before and after the attack.
Topics covered in Cyber Threat Intelligence include:
The constant change of the threat environment as capabilities, intent, opportunities, and defenses change and evolve
Different business models of threat actors, and how these dictate the choice of victims and the nature of their attacks
Planning and executing a threat intelligence programme to improve an organistation’s cyber security posture
Techniques for attributing attacks and holding perpetrators to account for their actions
Cyber Threat Intelligence describes the intelligence techniques and models used in cyber threat intelligence. It provides a survey of ideas, views and concepts, rather than offering a hands-on practical guide. It is intended for anyone who wishes to learn more about the domain, particularly if they wish to develop a career in intelligence, and as a reference for those already working in the area.
“Martin takes a thorough and focused approach to the processes that rule threat intelligence, but he doesn’t just cover gathering, processing and distributing intelligence. He explains why you should care who is trying to hack you, and what you can do about it when you know.”
―Simon Edwards, Security Testing Expert, CEO SE Labs Ltd., Chair AMTSO
Effective introduction to cyber threat intelligence, supplemented with detailed case studies and after action reports of intelligence on real attacks
Cyber Threat Intelligence introduces the history, terminology, and techniques to be applied within cyber security, offering an overview of the current state of cyberattacks and stimulating readers to consider their own issues from a threat intelligence point of view. The author takes a systematic, system-agnostic, and holistic view to generating, collecting, and applying threat intelligence.
The text covers the threat environment, malicious attacks, collecting, generating, and applying intelligence and attribution, as well as legal and ethical considerations. It ensures readers know what to look out for when considering a potential cyber attack and imparts how to prevent attacks early on, explaining how threat actors can exploit a system’s vulnerabilities. It also includes analysis of large scale attacks such as WannaCry, NotPetya, Solar Winds, VPNFilter, and the Target breach, looking at the real intelligence that was available before and after the attack.
Topics covered in Cyber Threat Intelligence include:
The constant change of the threat environment as capabilities, intent, opportunities, and defenses change and evolve
Different business models of threat actors, and how these dictate the choice of victims and the nature of their attacks
Planning and executing a threat intelligence programme to improve an organistation’s cyber security posture
Techniques for attributing attacks and holding perpetrators to account for their actions
Cyber Threat Intelligence describes the intelligence techniques and models used in cyber threat intelligence. It provides a survey of ideas, views and concepts, rather than offering a hands-on practical guide. It is intended for anyone who wishes to learn more about the domain, particularly if they wish to develop a career in intelligence, and as a reference for those already working in the area.
Martin Lee is Technical Lead of Security Research within Talos, Cisco’s threat intelligence and research organization. Martin started his career researching the genetics of human viruses, but soon switched paths to follow a career in IT. With over 20 years of experience within the cyber security industry, he is CISSP certified, a Chartered Engineer, and holds degrees from the Universities of Bristol, Cambridge, Paris-Sud and Oxford.
Publisher : Wiley; 1st edition (April 25, 2023)
Language : English
Hardcover : 304 pages
ISBN-10 : 1119861748
ISBN-13 : 978-1119861744
![]()
1、本站所有分享材料(数据、资料)均为网友上传,如有侵犯您的任何权利,请您第一时间通过微信(lib99net)、QQ(24661067)、电话(17898078618)联系本站,本站将在24小时内回复您的诉求!谢谢!
2、本站所有商品,除特殊说明外,均为(电子版)Ebook,请购买分享内容前请务必注意。特殊商品有说明实物的,按照说明为准。
![]()
![]()
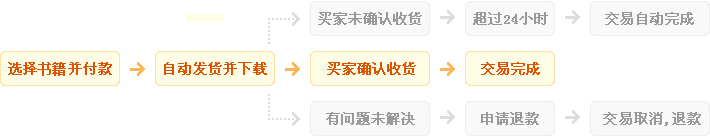
1、自动:在上方保障服务中标有自动发货的宝贝,拍下后,将会自动收到来自卖家的宝贝获取(下载)链接;
2、手动:未标有自动发货的的宝贝,拍下后,卖家会收到邮件、短信提醒,也可通过QQ或订单中的电话联系对方。
![]()
1、描述:书籍描述(含标题)与实际不一致的(例:描述PDF,实际为epub、缺页少页、版本不符等);
2、链接:部分图书会给出链接,直接链接到官网或者其他站点,以便于提示,如与给出不符等;
3、发货:手动发货书籍,在卖家未发货前,已申请退款的;
4、其他:如质量方面的硬性常规问题等。
注:经核实符合上述任一,均支持退款,但卖家予以积极解决问题则除外。交易中的商品,卖家无法对描述进行修改!
![]()
1、在未购买下前,双方在QQ上所商定的内容,亦可成为纠纷评判依据(商定与描述冲突时,商定为准);
2、在宝贝同时有网站演示与图片演示,且站演与图演不一致时,默认按图演作为纠纷评判依据(特别声明或有商定除外);
3、在没有"无任何正当退款依据"的前提下,写有"一旦售出,概不支持退款"等类似的声明,视为无效声明;
4、虽然交易产生纠纷的几率很小,但请尽量保留如聊天记录这样的重要信息,以防产生纠纷时便于网站工作人员介入快速处理。



 人工在线查找书籍,不要问我们有什么,告诉我们您需要什么即可...¥1.00
人工在线查找书籍,不要问我们有什么,告诉我们您需要什么即可...¥1.00 【PPT】Linear Algebra and Its Applica...¥0.1
【PPT】Linear Algebra and Its Applica...¥0.1 Delay-Adaptive Linear Control by Ya...¥29.99
Delay-Adaptive Linear Control by Ya...¥29.99 Handbook of Organic Materials for E...¥19.99
Handbook of Organic Materials for E...¥19.99 FinFET Devices for VLSI Circuits an...¥29.99
FinFET Devices for VLSI Circuits an...¥29.99 Positron Beams and Their Applications¥29.99
Positron Beams and Their Applications¥29.99 ASM Handbook Volume 11A Analysis an...¥420.00
ASM Handbook Volume 11A Analysis an...¥420.00 PETSc for Partial Differential Equa...¥29.99
PETSc for Partial Differential Equa...¥29.99 无机非金属材料热工设备-作 者 : 姜洪舟主编 2015第5版...¥14.99
无机非金属材料热工设备-作 者 : 姜洪舟主编 2015第5版...¥14.99 Product and Process Design Principl...¥9.99
Product and Process Design Principl...¥9.99